Secure Mobile Device Access with MobileIron Sentry and Kemp LoadMaster ESP

Thomas Stensitzki
Securing mobile devices access to an on-premises Exchange Server infrastructure without a hybrid setup is not complicated when using a single-vendor strategy. You simply implement a Mobile Device Management Solution and you are done. Enterprises doing business in the high security industry tend to follow a multi-vendor strategy to reduce the risks due to security flaws in third-party devices.
This post on the business requirement to authenticate mobile devices and authorize user access to on-premises Exchange Server mailboxes using a multi-vendor strategy. The solution consists of a MobileIron Sentry implementation and additional Kemp LoadMaster VLM devices located in an internal network segment. The Kemp LoadMaster Edge Security Pack (ESP) functionality is used to allow ActiveSync connections for members of a dedicated Active Directory security group only.
This results in the following four authentication and authorization endpoints:
- MobileIron access policies
- Kemp LoadMaster ESP security group membership validation
- Exchange Server ActiveSync client access allowance
- Exchange Server mobile device policy
Overview
The following diagram shows a simplified overview for mobile devices connecting to an on-premises Exchange Server. The perimeter and internal network segments are omitted for simplification reasons.
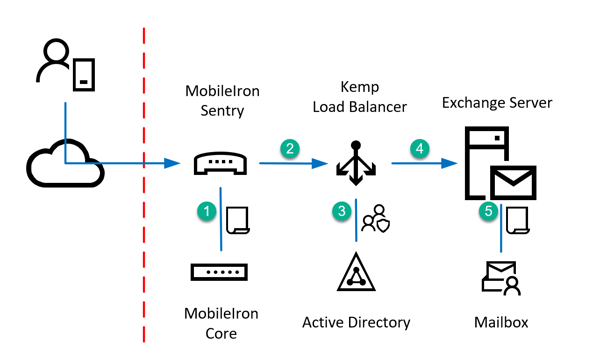
- A MobileIron managed device connects to MobileIron Sentry which validates access with MobileIron policies
- If a MobileIron policy allows access the device connects to Kemp LoadMaster ESP
- Kemp LoadMaster ESP configuration validates the security group membership of the authenticating user
- If the user is a member of the security group, the device connects to Exchange Server
- Exchange Server authenticates the user and checks, if the ActiveSync protocol is enabled and the device complies with Exchange Server MDM configuration
Kemp LoadMaster Virtual Service
The following screenshots illustrate a working setup for a virtual service load balancing mobile device connections from MobileIron Sentry to Exchange Server. I assume that you've already configured the Single-Sign-On (SSO) Domain settings for connecting to a domain controller to authenticate users.
SSL Properties
The SSL Traffic is offloaded and re-encrypted, because the LoadMaster needs to authenticate the user using the ESP feature. Therefore, you must ensure to select a Cipher Set that does not provide any weak or unsecure cipher suites. In this example I've selected the predefined set named BestPractices. Select the TLS protocol version depending on the compatibility level of the mobile devices used.
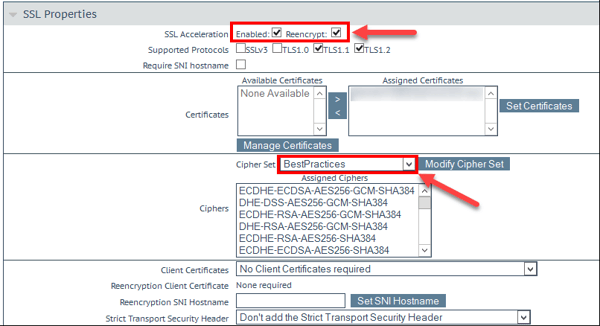
Ensure to click Modify Cipher Set to save the changes of the selected set of ciphers. Changes made to the checkbox selection do not need to be saved separately.
ESP Options
Open the ESP Options section and select Enable ESP to activate the ESP configuration. The required settings are as follows:
- Client Authentication Mode: Basic Authentication
Be aware that this setting requires that MobileIron users are provisioned using DOMAIN\SamAccountName notation and not the UPN Name - SSO Domain: An existing SSO Domain configuration for user authentication
- Allowed Virtual Hosts: The FQDN matching the Load Master virtual service IP address accessed by MobileIron Sentry to connect to Exchange Server
- Allowed Virtual Directories: Can be limited to /Microsoft-Server-ActiveSync otherwise leave the default /*
- Permitted Groups: The name of the Active Directory security group(s) containing the allowed users for mobile device access
- Server Authentication Mode: Basic Authentication
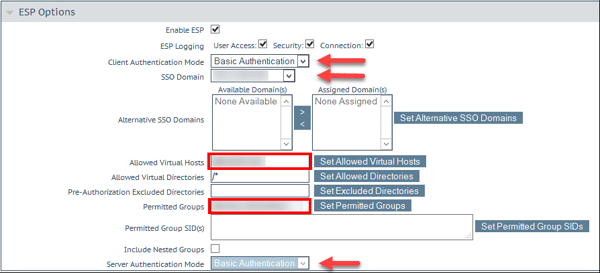
Do not forget to click the Set button where available.
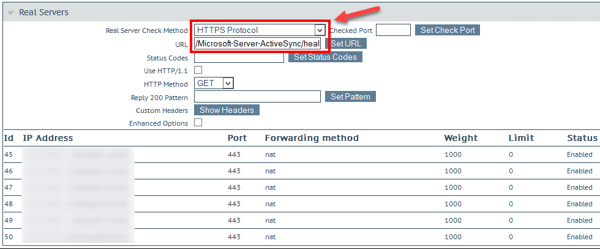
Real Servers
In the Real Servers section, you add all member servers of your Exchange Server DAG or any other Exchange Servers serving client access functionality. Ensure to use the HTTPS protocol for health checks and ensure to query the /Microsoft-Server-ActiveSync/healthcheck.htm url.
With this Kemp LoadMaster configuration, you've added a Kemp LoadMaster as an additional authentication endpoint to secure mobile device access to Exchange Server mailboxes. This implements a multi-vendor strategy for authorization and authentication of mobile devices and users.

Thomas Stensitzki
Related Posts


Securing Exchange Servers

Nathan O'Bryan MCSM
Securing Exchange Servers
Securing Exchange servers is hard. I mean it can be a giant pain...


