Azure Active Directory Monitoring: Domain Services
Introduction to Identity
With organizations moving workloads to the cloud, they no longer have the...


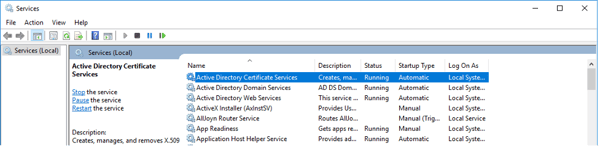
In the previous article we looked at the operations and processes regarding backup and recovery of AD DS information, namely the AD DS database and its objects. In this article we will be looking at the backup options for some of Active Directory’s other modules such as Active Directory Certificate Services (AD CS). Your Active Directory monitoring solution should be tracking events for AD CS to ensure the information is backing up successfully.
Secure Socket Layer/Transport Layer Security
Your Microsoft organization’s public key infrastructure (PKI) will most likely be based off of AD CS. Your PKI is responsible for maintaining your certificate infrastructure which is used for securing your software systems. Digital certificates will provide confidentiality through encryption, infrastructure integrity through digital signatures, and authentication using certificate keys with clients, users, or device accounts through AD on your network. AD CS enhances your security through the binding of the identity of a person service, or device to a private key and is a critical component of your Active Directory Monitoring. AD CS is a secure, cost-effective, and efficient way to distribute certificates through your infrastructure. Certificates can be used by many systems in your organization including but not limited to:
What do you need to back up on your certificate server? Well let’s look at it in the simplest terms and go from there. You will need to back up the entire Certificate Authority (CA) database, the certificate, and the private key that the CA is currently using, the AD database, and most administrators will recommend a full system backup using the tool of your choice. Let’s look at these options individually.
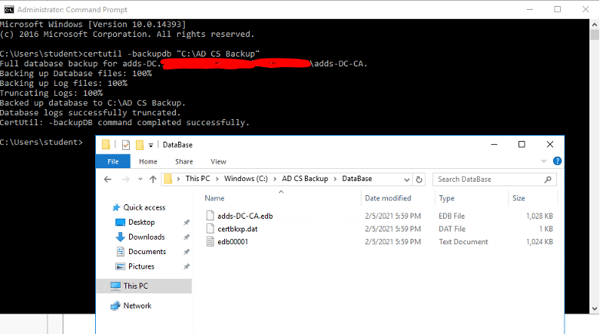
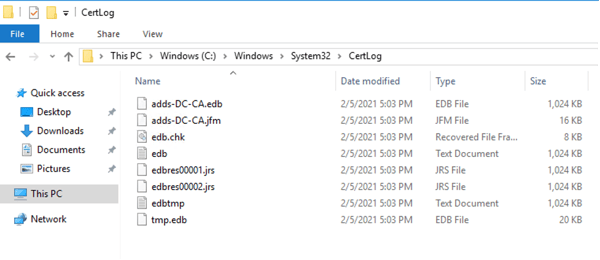
The database file name will be the CA name followed by the extension “.edb”. The CA database structure uses the Microsoft Jet Database for all transaction level processing, storage, and rollback protection. What files are associated with the CA?
The log file syntax starts at edb00001.log and extends to edbfffff.log. Each log file is 1MB in size. When all the space is consumed, the next log file is created. This will give you around 1TB of log space. Now, what about when you use up all your space? The good news is that as long as you are running backups the files will be truncated (cleaned). Files are truncated when either one of two conditions occur:
1. A backup is performed on the CA using either the GUI, VSS, or the command line using Certutil -backupDB.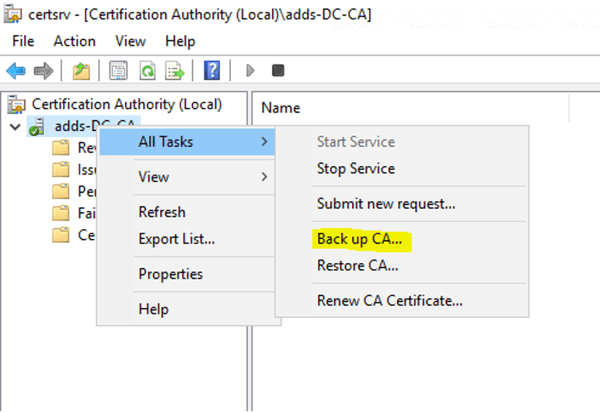
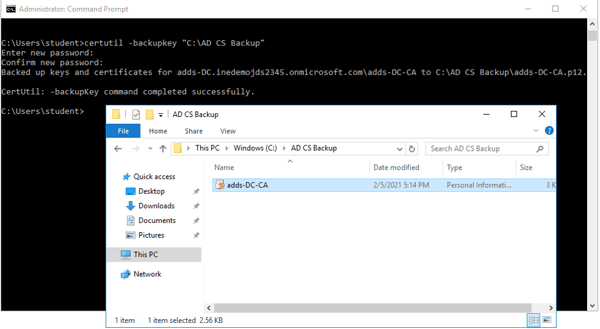
Having a quick copy of the certificate from the CA is never a bad thing as long as it is up to date and stored in a secure location with limited access. You can run the Certutil -backupKey command on the CA to ensure you have a copy of the certificate and private key that the CA is currently using to a PFX file. You will be able to specify the folder location of your choosing.
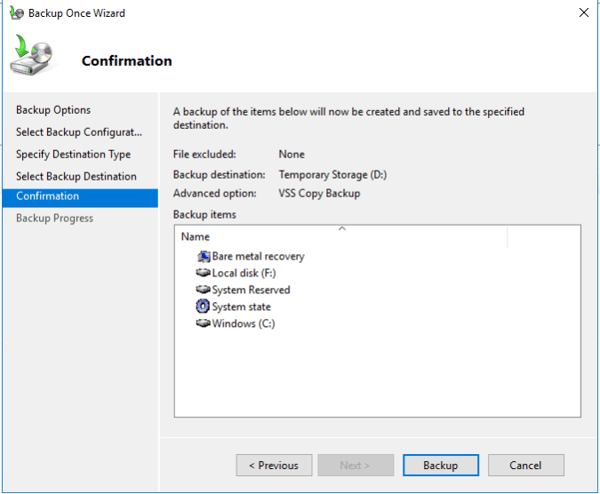
It is always recommended to perform full system backups whether using the Windows Backup tool or using a backup solution of your choosing. Be sure to include all critical volumes and the System State. The critical volumes should include any and all folders that were included in the Certutil commands.
This can be achieved by running the full back up as described above. Just make sure you include the critical volumes that have the NTDS.dit database instance as well as the system state. You really should not rely on replication if you are recovering from a major accident or outage. Any changes may have replicated from the bad database to other AD DS instances in your environment.
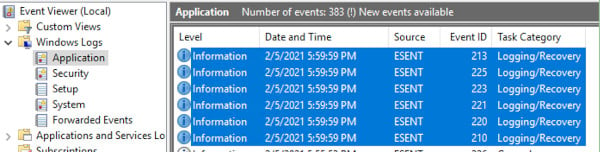
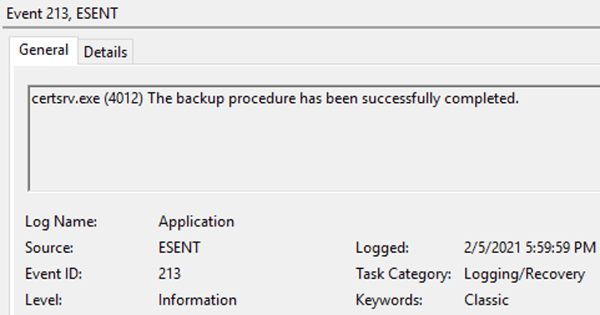
One of the easiest ways to see if your backup and log truncation completed successfully is to check the Event Viewer. More Specifically, check the Windows Application logs. After running the Certutil -backupDB command, you will want to look for event 213 with the source “ESENT”. Event 210 is when the backup started. Your Active Directory Monitoring solution should be looking for these events and, if you choose, looking for the events ranging from ESENT 210 – 225. If you are using ShadowCopy you will want to monitor for ESENT events 2001-2006.
You should consider running a local script to perform a scheduled backup of your Certificate Authority. You can use whatever language you like for your script, but it needs to be able to back up the following:
You may want to check the PowerShell Gallery from Microsoft for scripts created by Microsoft MVPs. [Always test scripts in a non-production environment. Never test in production environments.]
.
Active Directory is the foundation of your network, and the structure that controls access to the most critical resources in your organization. The ENow Active Directory Monitoring and Reporting tool uncovers cracks in your Active Directory that can cause a security breach or poor end-user experience and enables you to quickly identify and remove users that have inappropriate access to privileged groups (Schema Admins, Domain Administrators). While ENow is not an auditing software, our reports reduce the amount of work required to cover HIPAA, SOX, and other compliance audits.
Access your FREE 14-day trial to accelerate your security awareness and simplify your compliance audits. Includes entire library of reports.

Jonathan is an Information Technology consultant and instructor that specializes in migrations, security audits, new Microsoft technology implementations, and support contracts for Microsoft technologies. Jonathan also has expertise in Office 365 Services including, but not limited to, Azure Active Directory, Exchange Online, Skype for Business/Teams, SharePoint Online/OneDrive, Microsoft Azure/Office 365 Security and Compliance features including alerts, permissions, information classification, data loss prevention, information governance, threat management, data privacy, and reporting.


With organizations moving workloads to the cloud, they no longer have the...


In Part 2 of this series, we'll discuss backup and recovery options for Active Directory Domain...