Recap of ENow’s webinar discussing the importance of Active Directory Monitoring & Reporting, and best practices that can be implemented with a robust Active Directory Monitoring tool
Monitoring the vitals of Active Directory is crucial for the network health and security of any organization. However, there’s a big difference between Active Directory monitoring and Domain Controller monitoring. There’s also a big difference between monitoring and reporting, and both are necessary to ensure Active Directory doesn’t become a liability for your organization.
To help IT Pros learn more about the intricacies of monitoring Active Directory, ENow hosted a webinar on the topic with Sander Berkouwer, Microsoft MVP, and Jay Gundotra, Technical Founder & CEO of ENow.
Couldn’t attend this time? We’ve got you covered. Below you’ll find some key takeaways from the webinar, as well as a recording of the webinar.

The Reach of Active Discovery
Jay and Sander reviewed several real-life examples that can have a catastrophic effect on your organization. Scenarios where Domain Controllers were unresponsive; when Group Policy was used as an attack surface by adversaries to configure settings and push malware; and times when data in Active Directory is inconsistent and Domain Controllers aren’t replicating. They also discussed the ways you can proactively mitigate these issues with the proper Active Directory monitoring tool.
Domain Controller Monitoring & Active Directory Monitoring
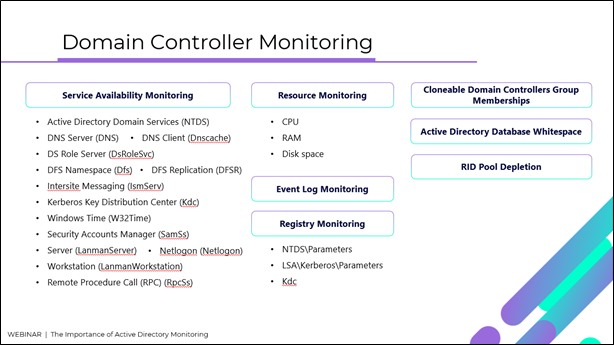
Domain Controller Monitoring is important when assessing the overall health of Active Directory, as these are not mere nodes offering the ‘Active Directory’ application. There are files, registry settings and services that are critical to the way Active Directory is hosted on Domain Controllers. With an Active Directory Monitoring tool, Domain Controllers are monitored as the Active Directory hosts, inspecting core components such as service availability, disk space, resource status, event logs and registry monitoring. This enables you to identify the root cause of any issues that center around Active Directory’s availability and integrity.
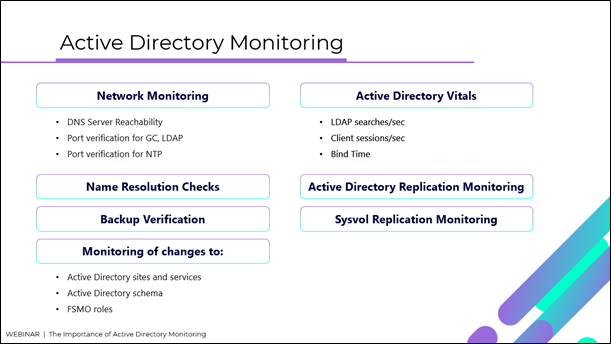
Whereas Active Directory is monitored as a network service, providing critical information around network stability and security, name resolution checks, Active Directory vitals, backup verification and replication monitoring.
Monitoring vs. Reporting
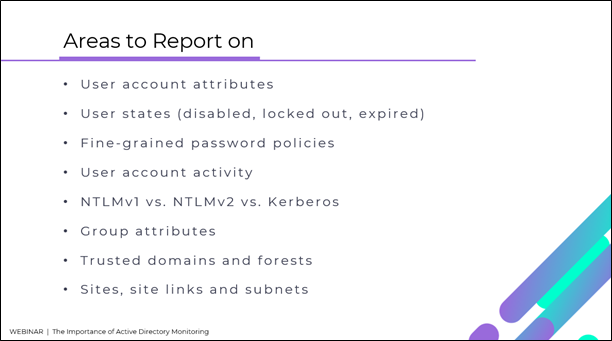
Active Directory Monitoring tools can spot resource and configuration problems as they happen so admins can remedy them as fast as possible. Beyond the ability to select and filter, Active Directory Reporting enables admins to discover trends around how Active Directory is performing currently, and how it could potentially fail years from now.
With the ENow Active Directory Monitoring and Reporting tool you get all the functionality that Jay and Sander talk about in this session. It automatically performs health checks to ensure that your Active Directory is healthy. It simplifies troubleshooting for name resolution, network, replication and DNS issues before they become bigger problems for you. It uncovers cracks in your Active Directory that can cause a security breach or poor end-user experiences, enabling you to quickly identify and remove users that have inappropriate access to privileged groups (Schema Admins, Domain Administrators). While ENow is not an auditing software, our reports reduce the amount of work required to cover HIPAA, SOX, and other compliance audits.
Access your FREE 14-day trial to accelerate your security awareness and simplify your compliance audits. Includes entire library of reports.