Security Improvements in SharePoint Online and OneDrive for Business
Over the past few months, some significant improvements have been made around the external sharing...


It’s been a while since we covered SharePoint Online and OneDrive for Business, and some major improvements have arrived. The new group-backed team sites are now available, including a preview of the ODFB admin portal and conditional access. Here are important additions to restricting user access and securing external collaboration.
The preview of the ODFB admin center was announced a few weeks ago. The new portal gives administrators an easy-to-use, UI-based tool that brings together most of the settings available with PowerShell, the SPO admin center and Intune admin console.
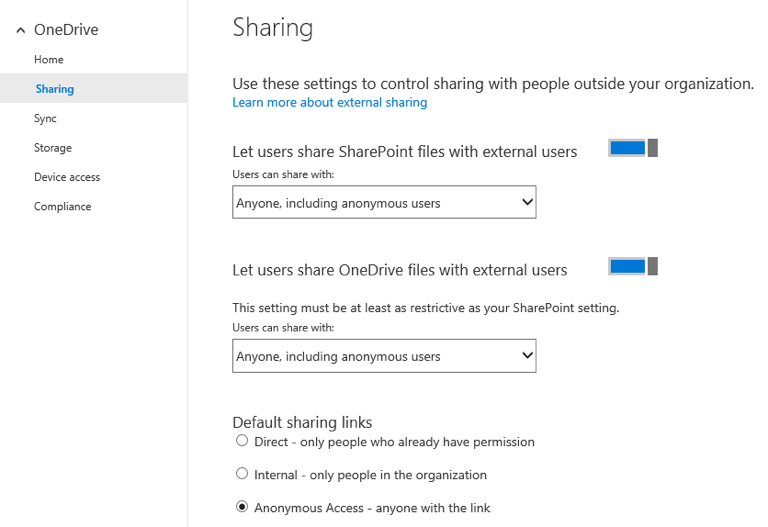
The portal features several different sections. Home gives you a brief introduction and the feedback link, and the Sharing section exposes different sharing controls similar to the SPO admin center. You can turn external sharing on or off, control new user invitations and guest links and set the default type of link generated when you press the “Share” button. You can also restrict sharing to specific external domains or block selected ones. Other settings include the lifetime of guest links and controlling the (re)share functionality for external users.
Some settings are still not exposed in the UI, including:
Those settings are available in the SPO admin center under the Sharing tab, or can be configured via PowerShell. An unfortunate bug with the setting to limit external sharing to select group of users only caused its removal from the ODFB admin center, but hopefully it will be back soon.
Sync covers settings related to the sync client. You have the option to disallow downloading of the client, restrict syncing to specific domains and block some file types. The Storage section allows you to configure the default quota for ODFB sites and retention for deleted sites. The options to configure a secondary owner and access delegation are not exposed here. You still should configure those in the SPO admin center.
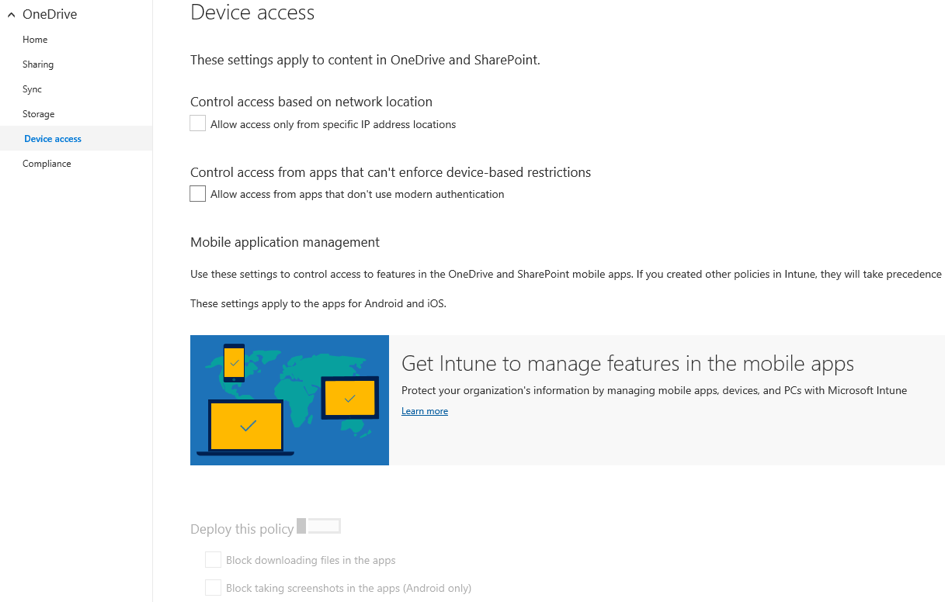
The Device Access section exposes some of the more interesting settings, including the ability to allow access only from specific network location. This was one of the most requested features since Office 365 reached general availability — the “available anywhere, anytime, on any device” design was problematic for customers in sensitive industries.
Until recently, restrictions were only possible when AD FS was in place and had some undesired side effects. Now administrators can define a set of allowed IPs (or ranges) and configure SPO/ODFB to only allow access from those IPs. The functionality became available in November via PowerShell and the Set-SPOTenant cmdlet and is now also exposed in the ODFB Admin center. Unlike conditional access, this feature does not require Azure AD Premium subscription or any additional licenses.
Under the mobile application management group, you can enforce a variety of settings on ODFB apps for iOS and Android, such as blocking file downloads, the copy/paste functionality and restricting access to specific approved apps.
They are the same settings exposed in the Intune console and require a valid EMS/Intune subscription. If the subscription is not provisioned in your tenant, those settings unfortunately aren’t available (see screenshot below). Detailed description on the different MAM settings can be found here.
The last section of the portal Compliance includes links to different auditing, retention, DLP and eDiscovery settings available in the Security and Compliance center.
Unfortunately, many of the cool features announced at Ignite are still under development or in limited preview, so we can’t explore them yet. Here are the features that made it into production:
Other interesting features announced at Ignite include:
Restricting downloading, syncing, editing and printing of files from web browsers. Instead of using conditional access to completely block access for non-domain joined or non-compliant devices, you can use a “read-only” configuration. The new “read-only” option and additional settings in the currently missing User Access section of the SPO/ODFB portals were showcased at Ignite, but aren’t live yet. Here is a screenshot of the upcoming settings taken from the Ignite session:
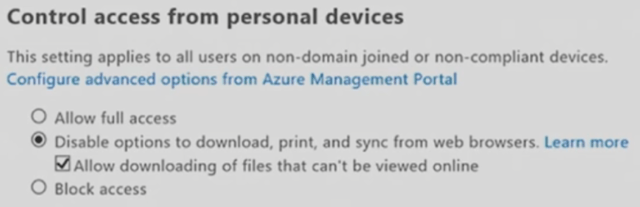
Cool feature, right? Keep an eye out for the new User Access section in the SPO/ODFB admin portals!
In the compliance area, DLP policy tips are coming to the mobile apps. Policy tips are also visible directly in the Share dialog in browsers displayed with additional information why the match was triggered.
With the introduction of Azure Information Protection and latest improvements in the Security and Compliance center, we will soon have global, unified experience across all workloads for data retention, classification/labeling and records management.
Tag a document with the “confidential” tag, and it will not only be preserved for X amount of days, but other actions will also apply. These include making sure the document is deleted after the mandatory retention period has expired, it’s encrypted and external sharing is blocked. Watch this Ignite session for more info if you haven’t done so already.
BYOK support for the per-file encryption utilized across SharePoint Online is also coming soon, with no effect on SPO’s ability to “reason over data.”
You should now have an overview of the newly introduced OneDrive for Business Admin Center with the options available and important controls for restricting user access and managing compliance features for SharePoint Online and OneDrive for Business.
Some of the new features are already available, while others will be coming over the next few months. The lists above are not exhaustive, and Microsoft’s continuous focus on security and compliance will surely drive even more improvements this year.
Other Ignite sessions you don't want to miss:
Keep your OneDrive and SharePoint content safe
Protect your OneDrive and SharePoint files on mobile devices

Vasil has been actively involved with Office 365 for over four years now. He spent over an year as Support Engineer for Microsoft Online Services with one of Microsoft's vendors, working with BPOS and Office 365 customers. Switching sides, he later held support positions with several multinational enterprises, before finally moving to a consultant role. This varied experience allows him to have an unique perspective on the ins and outs of the Office 365 suite. He has closely followed the evolution of Microsoft's cloud offerings, starting with BPOS, with expertise covering all stages of the Office 365 lifecycle. He holds a charter member certification for Office 365 (MCITP and MCSA), and has been awarded as Microsoft MVP for second year in a row.


Over the past few months, some significant improvements have been made around the external sharing...


Protecting corporate data is one of the most important tasks of our time. Microsoft 365 helps you...