Identity and Authentication Management for Office 365
The good people at ENow asked me to do a webinar on Identity and Authentication Management for...

Lightweight Directory Access Protocol (LDAP) is a directory service protocol that is used to search for information within your Active Directory and a useful tool that can better assist you with Active Directory Monitoring. LDAP is used to search your active directory for information about users, computers, and groups within your Active Directory database. LDAP queries can be run from multiple different tools including PowerShell, ldapsearch, VB Scripts, and the saved queries feature in Active Directory Users and Computers.
But what exactly are LDAP queries? How do they work and how can you ensure that your Active Directory is properly setup to support the quickest and most accurate LDAP queries possible? Lastly, what troubleshooting steps can you take when you discover that you're getting slow results with LDAP queries in your AD.
This seems like a good place to start. What do LDAP queries do for me?
Anytime you search Active Directory for information like who is in a specific group, or what groups are there, or information from a specific user's account, that search is completed via an LDAP query. That query may be done from within Active Directory Users and Computers (ADUC), PowerShell, or many other tools. LDAP is the protocol that Active Directory uses to answer questions about what’s in your Active Directory database.
For the most part, we do not think of these searches are “LDAP queries” because we just open ADUC, go to a group, and then see who is in that group.
You can run more customized LDAP queries from within ADUC. To do so, first open ADUC.
Right click on “Saved Queries” > New > Query
In your new query, give it a name and then select “Define Query”
Now select “Custom Search” from the drop down at the top, and go to the “Advanced” tab.
Here you can enter any custom LDAP query you would like. The format for these LDAP queries is defined in RFC 4515. That being said, no one wants to figure out how to write up these LDAP queries. To make life a little easier for you, I have listed below some of the LDAP queries I like to setup for my customers.
Saved ADUC Query |
LDAP Filter |
| Users with the “Password never expires” option enabled | (objectCategory=person)(objectClass=user)(userAccountControl:1.2.840.113556.1.4.803:=65536) |
| Users who have not changed their password for more than 3 months | (&(sAMAccountType=805306368)(pwdLastSet<=132161330597286610)) |
| Find users who have “Sales” in the department field | (&(objectCategory=person)(objectClass=user)(department=*sales*)) |
| Users with the empty Profile Path attribute | (objectcategory=person)(!profilepath=*) |
| Active user accounts with expired passwords | (objectCategory=person)(objectClass=user)(pwdLastSet=0)(!useraccountcontrol:1.2.840.113556.1.4.803:=2) |
| All AD users, except disabled | (objectCategory=person)(objectClass=user)(!useraccountcontrol:1.2.840.113556.1.4.803:=2) |
| Locked AD user accounts | (objectCategory=person)(objectClass=user)(useraccountcontrol:1.2.840.113556.1.4.803:=16) |
| Users with e-mail addresses | (objectcategory=person)(mail=*) |
| Users without e-mail addresses | (objectcategory=person)(!mail=*) |
| Users hidden from the Exchange Address Book (GAL): | (&(sAMAccountType=805306368)(msExchHideFromAddressLists=TRUE)) |
| The list of accounts never logged on to the domain | (&(objectCategory=person)(objectClass=user)(|(lastLogonTimestamp=0)(!(lastLogonTimestamp=*))) |
| User accounts created in a specific time period (in 2019) | (&(&(objectCategory=user)(whenCreated>=20190101000000.0Z&<=20200101000000.0Z&))) |
| AD users created this year | (&(&(&(objectClass=User)(whenCreated>=20200101000000.0Z)))) |
| Computers running Windows 10 | (&(objectCategory=computer)(operatingSystem=Windows 10*)) |
| Computers running a specific Windows 10 build (for example Windows 10 1909 have build number 18363) | (&(&(objectCategory=computer)(operatingSystem=Windows 10*)(operatingSystemVersion=*18363*))) |
| Find all Windows Server 2016 except domain controllers | (&(&(objectCategory=computer)(!(primaryGroupId=516)))(operatingSystem=Windows Server 2016*)) |
| All Microsoft SQL servers | (&(objectCategory=computer)(servicePrincipalName=MSSQLSvc*)) |
| All Exchange distribution groups | (&(objectCategory=group)(!groupType:1.2.840.113556.1.4.803:=2147483648)) |
| Find AD object with a specific SID | (objectSID=S-1-5-21-87654321-12345678-5566443311-1231) |
LDAP queries can be problematic when they are slow or use too many resources. The ones I have listed above are not likely to be a problem, but there are many applications that may be running LDAP queries in your AD environment that can be problems.
Troubleshooting LDAP queries that are taking excessive resources in your AD can be very difficult. To make it a bit easier, I am going to give you a quick guide for what to do if you suspect you have LDAP queries that are causing problems. Before we get into those instructions, keep in mind that we will be turning on a high level of logging for this. It is not a great idea to leave this logging running when you are done with it.
Enable 1644 metadata collection - Configure registry keys for Field Engineering to 5 (HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\NTDS\Diagnostics\15 Field Engineering)
Configure registry entries for expensive, inefficient, and long running LDAP queries -
| HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NTDS\Parameters\Expensive Search Results Threshold | DWORD | 10,000 |
| HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NTDS\Parameters\Inefficient Search Results Threshold | DWORD | 1,000 |
| HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NTDS\Parameters\Search Time Threshold (msecs) | DWORD | 30,000 |
Collect and analyze data – Once those registry settings are made on a domain controller, let it run and collect data. I would recommend about 30 minutes or so.
LDAP queries can be extremely useful for gathering specifically organized information from Active Directory. When LDAP queries take too long or too many resources, troubleshooting them can be difficult. Hopefully this blog will make both using LDAP queries and troubleshooting problem queries a little bit easier for you.

Active Directory is the foundation of your network, controlling access to your organization's most critical resources. The ENow Active Directory Monitoring Tool, with comprehensive reporting, identifies vulnerabilities in your Active Directory that could lead to security breaches or poor user experiences. It helps you quickly find and remove users with inappropriate access to privileged groups like Schema Admins and Domain Administrators. While ENow is not an auditing software, our comprehensive reports significantly reduce the effort needed for HIPAA, SOX, and other compliance audits.
Start your complimentary 14-day trial of ENow's Active Directory Monitoring Tool to enhance your security awareness and streamline your compliance audits. The trial includes full access to our report library.

Nathan is a five time former Microsoft MVP and he specializes in Exchange, Microsoft 365, Active Directory, and cloud identity and security.


The good people at ENow asked me to do a webinar on Identity and Authentication Management for...
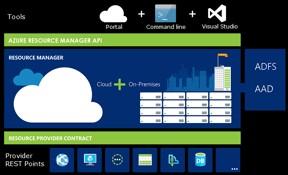

Azure Resource Manager (ARM) is Microsoft's platform for deploying and managing resources within...