Restricting Access to Security and Compliance Center Functionalities
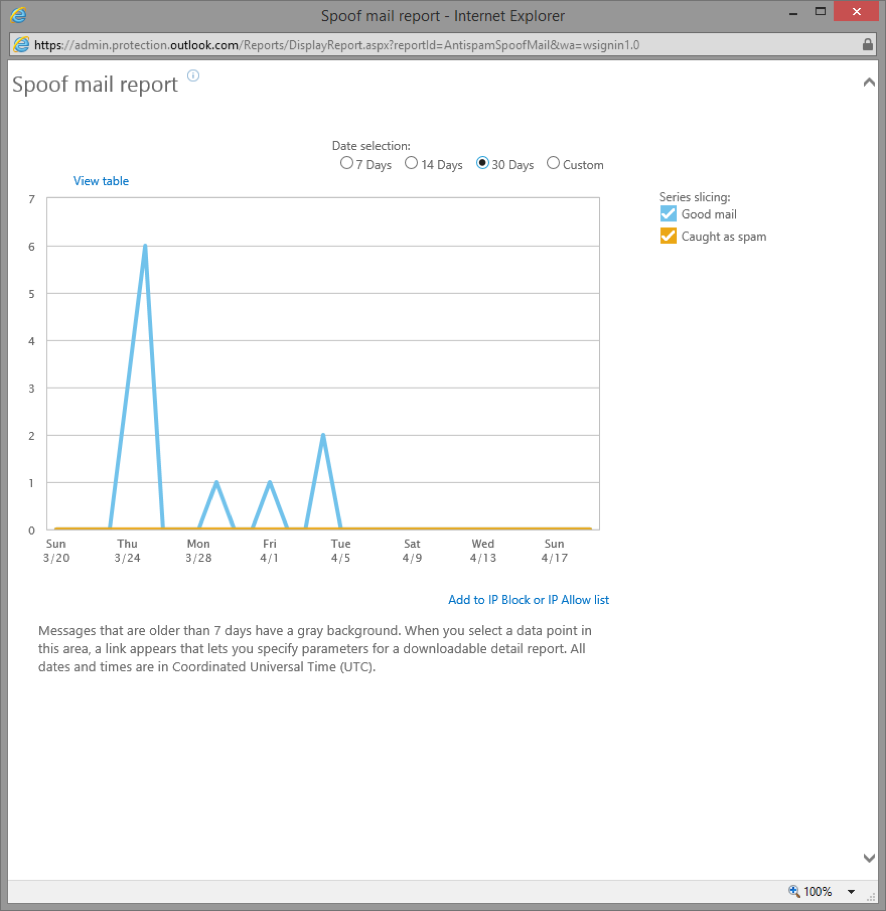
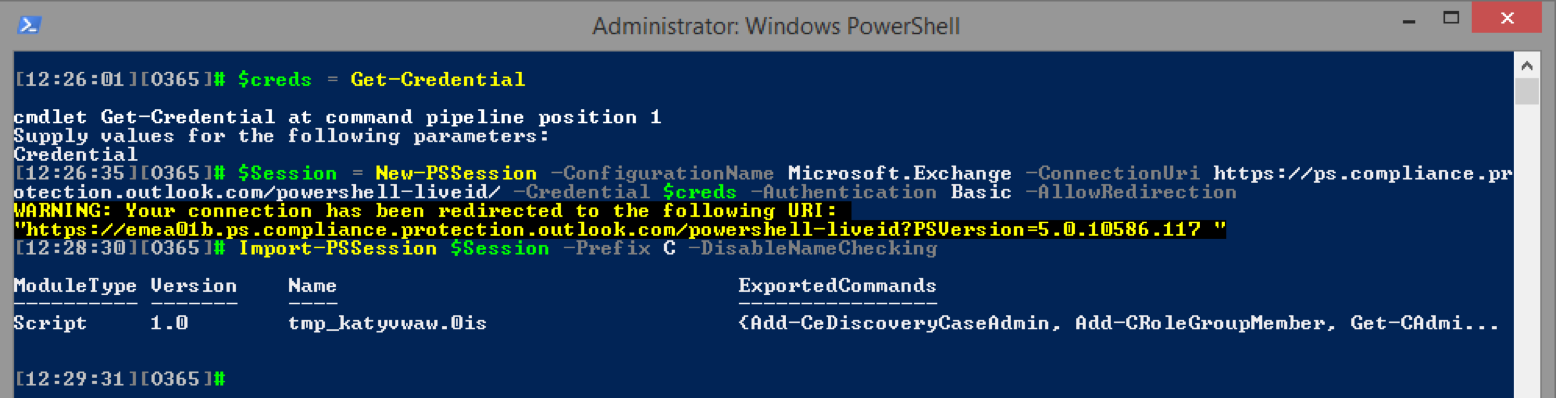
About a year ago, we published an article on how to manage preservation policies in the new Security and Compliance Center in Office 365 via PowerShell. Over the course of the last year, a great number of new features have been added to the SCC, which is now the central place for data governance in Office 365. With some minor exceptions, all of the functionalities exposed in the SCC are very sensitive and controlling access to them is vital. In this article, we will cover some methods to restrict access to the SCC features. By using PowerShell, of course!