Preservation Policies in Office 365
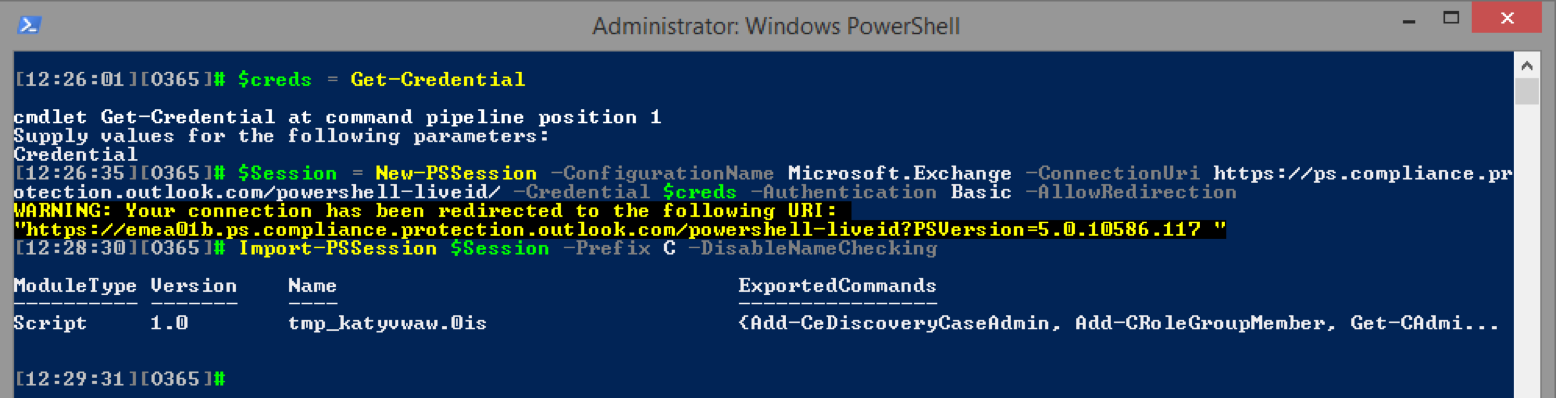
Preservation policies were introduced almost a year ago as part of the Compliance Center in Office 365 (which you might also know as the Protection center, or as Security & Compliance Center after the latest rebranding). In a nutshell, they allow you to preserve content across (almost) all Office 365 workloads. They also provide support for true immutability of the data, such that even the company administrators cannot override.