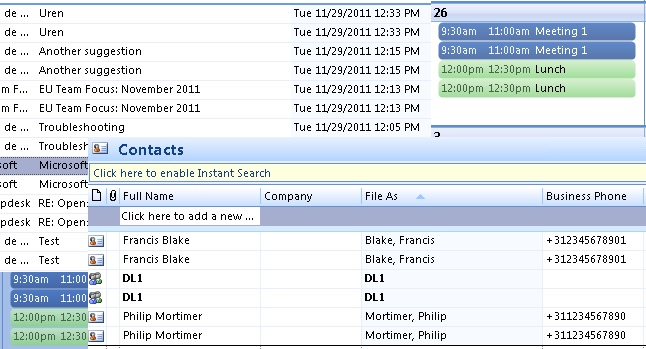
Exchange Monitoring: Disk Space
Disk space is vital to the health of an Exchange Server. Without disk, you don’t have email, thus Exchange monitoring - disk space is vital. Exchange is dependent on having disk because every time an email is sent it’s written to disk, without it you’re S.O.L.